Achieving Your Business
Goals Through Data Collabration
Goals Through Data Collabration
-
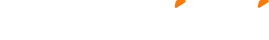
 Drive Revenue Growth
Drive Revenue Growth -
 Analyze and Acquire New Customers
Analyze and Acquire New Customers -
 Determine Market Segmentation
Determine Market Segmentation -
 Accelerate Product Development
Accelerate Product Development -
 Enhance Research and Development
Enhance Research and Development